Below we will analyze the main methods of viewing the latest events in your computer and tell you about the traces that every Windows user leaves behind.

Contents
- History of the browser.
- Browse the modified files.
- Search for deleted data in the Recycle Bin.
- Browsing the "Downloads" folder.
- Checking the latest installed programs.
- Search for the most recently launched programs.
- Additional methods to find the latest actions.
- What to do if important data was deleted during unauthorized access?
The Windows operating system and many of the programs running inside it leave many traces that can be used to determine what was happening with the computer while the user was away. This guide will help you identify where someone went, what they saw, what programs were running, and what files was changed when they unauthorized accessed your system.
Viewing the latest actions is a complex measure that requires one after another to check individual elements of the system and software, where traces may have been left after access to a third party’s PC.
History of the browser.
The first thing to do is check the history of your Internet browser, where the addresses of the sites to which the transition from the browser were made are always saved.
The browser history should be checked first of all. It is because it can be used to obtain data for logging into social networks, bank accounts, online services of digital distribution accounts (for example, Steam, Origin, Epic Games Store, etc.) and other services from which attackers can obtain payment card data and other material benefits.
To view the history of Google Chrome, just open the browser and press “Ctrl+H”, or enter the path “chrome://history/” in the search box or click on the three points icon in the upper right corner and select “History” in the menu that opens.
In the window that opens, you can view the date, time, and resources visited to determine what third parties were looking for when unauthorized access to your PC.
If you find that the browser history has been cleared even though you didn’t do it, it means that someone tried to hide the traces of the computer during the unauthorized access.
In this case, you should use our guide “How to restore browser history after cleaning“, where you can learn about restoring and viewing the history in all popular browsers.
In addition to the history, Google Browser saves many actions taken online from your computer in a special section “My Actions”, where you can find out more details about entered search requests, watched YouTube videos, and other information.
To go to the menu “My Actions”, just copy and paste into the address bar the link https://myaccount.google.com/activitycontrols Then select the desired item (for example, select the item “Application History and Web Search”, but here you can also view the history of locations, history of views and searches YouTube, data from synchronized devices, etc.) and click on the button “History Management”.
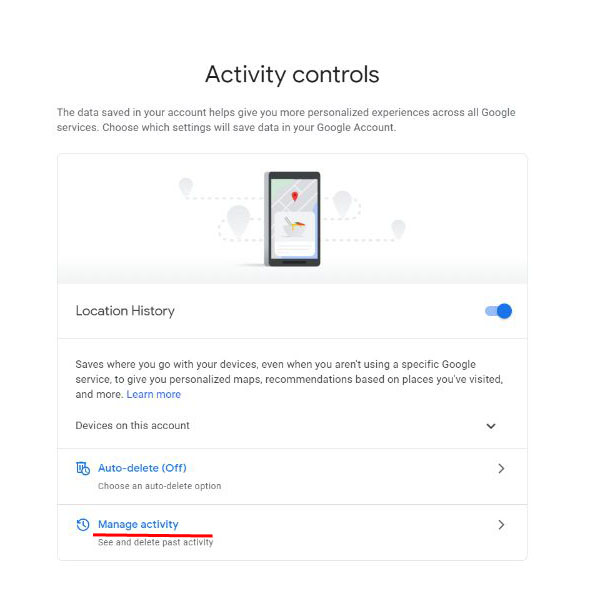
In the window that opens, you can see in detail all the actions, views, and entered search queries that have been performed recently.
Browse the modified files.
After reading the history in your browser, you should begin to identify the actions performed directly with the computer and personal information.
To view files, documents, and other data that have been modified during unauthorized access, you should use the name file viewer.
To do this, it is necessary:
Step 1: Right-click on “Start” and select “Run” in the menu that opens. In the field of the opened window, enter the command “recent” and confirm the action “OK”
Step 2: In the window that opens, you can find the latest files, photos, documents, and other data with which you performed any actions, as well as the exact date of their modification.
It should be noted that “hackers” can delete all data from this folder, but it will be a clear trace of third parties activities with the system and information.
Search for deleted data in the Recycle Bin.
If any data was deleted during unauthorized access to your computer, it could go to the Recycle Bin, where you can see the deletion time and quickly restore deleted files.
With the default, Windows interface settings, the Recycle bin is always located on your desktop.
Suppose there are suspicions that the files were deleted during unauthorized access, and the trash was cleaned up. In that case, we recommend you urgently familiarize yourself with the topic “How to recover files after deleting them to the Recycle Bin and cleaning it up“. If you do not recover the data immediately, it may be destroyed soon due to overwriting!
Browsing the “Downloads” folder.
In addition to the Recycle Bin, you should also check the “Downloads” folder, as it may contain the latest data downloaded to your computer from the Internet.
It can be both malicious programs and special utilities for surveillance, as well as other malicious and dangerous software that can harm the system and user privacy. The easiest way to navigate to “Downloads” folder is to use “My Computer” or “This PC” in Windows 10.
In the window that opens, you should carefully check the downloaded installation data and other suspicious files. If they are found, you should remove them immediately, because running executable files can lead to infection.
Checking the latest installed programs.
During unauthorized access to your computer, third-party programs, maintainers, adware, and other unwanted software may have been installed in the system, so you should check the recently installed programs.
To do so, you should:
Step 1: Left-click on the “Search” icon (the magnifying glass image near the “Start” button) and enter the phrase “Control Panel” into the line, then go directly to the “Control Panel” itself. The other way to open Control Panel is: right-click on “Start” and select “Control Panel”
Step 2: While in the control panel, switch on the display mode “Category” and press the “Uninstall a program” item.
Step 3: In the list that opens, click on the “Installed On” column to align the list of programs with the installation date, and then carefully review all recently installed programs for suspicious ones.
When detecting unknown utilities, the best solution is to remove them. It can be done by double left-clicking in the list. Important: This window may display system programs and utilities, so you should know what to delete and what is better left.
Search for the most recently launched programs.
Windows also allows you to find out what time and what programs were running, which will help you better understand what was happening during unauthorized access.
To take advantage of the search for the most recently launched programs, it is necessary:
Step 1: Go to the “This PC” directory and in the upper right corner enter “.exe” – the key that will allow you to find all executable files on your computer.
Step 2: Right-click on any of the columns in the list and select “Sort by” in the menu that opens, and then “more”
Step 3: In the menu that opens, tick the “Access Date” item to align the list with the last launched program executive files.
Additional methods to find the latest actions.
In addition to the methods described above, advanced users will be able to browse through the Windows logs, which allow them to find when various applications were running or when logging on and off.
It should be noted that the event log is a tool designed for system administrators, so users who do not know the codes of specific events will not be able to find the necessary information in the logs.
In addition to the methods described above, it is possible to use special programs to monitor the computer on a permanent basis (for example, NeoSpy, Snitch, Actual Spy, and others). In this case, the utilities will show all the computer’s actions in a convenient menu and in a form understandable to any user.
What to do if important data was deleted during unauthorized access?
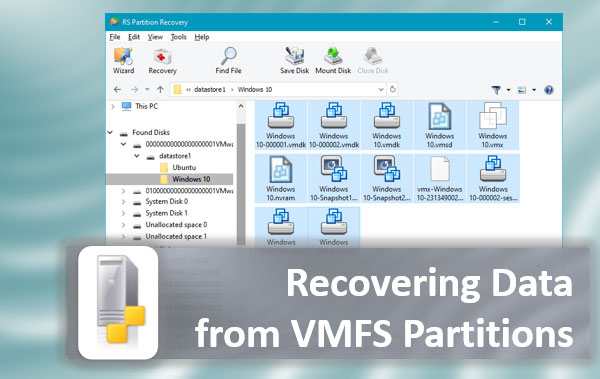
If you find that someone intentionally deleted important data, photos, documents, or any other information from your computer. In that case, we recommend you to immediately use a special utility to restore the data — RS Partition Recovery.
With this utility, you can quickly return data that has been deleted with the Shift+Delete key combination, formatted from the drive, deleted by viral software, or destroyed during a change of the drive’s logical structure.
RS Partition Recovery has extremely low system requirements, which allows the program to be used even on laptops and office machines. Besides, the data recovery utility has an intuitive interface, which can be understood by absolutely any user.
To recover lost files, you only need to perform a quick or full analysis of the disk. It will help to identify recently deleted files or all data that can be recovered. To learn more about other features and benefits of work with RS Partition Recovery, we recommend you visit the program’s official webpage.